
You have been successfully subscribed!



Gain a competitive edge. Our AI solutions help you work smarter, move faster, and deliver more value to your customers.
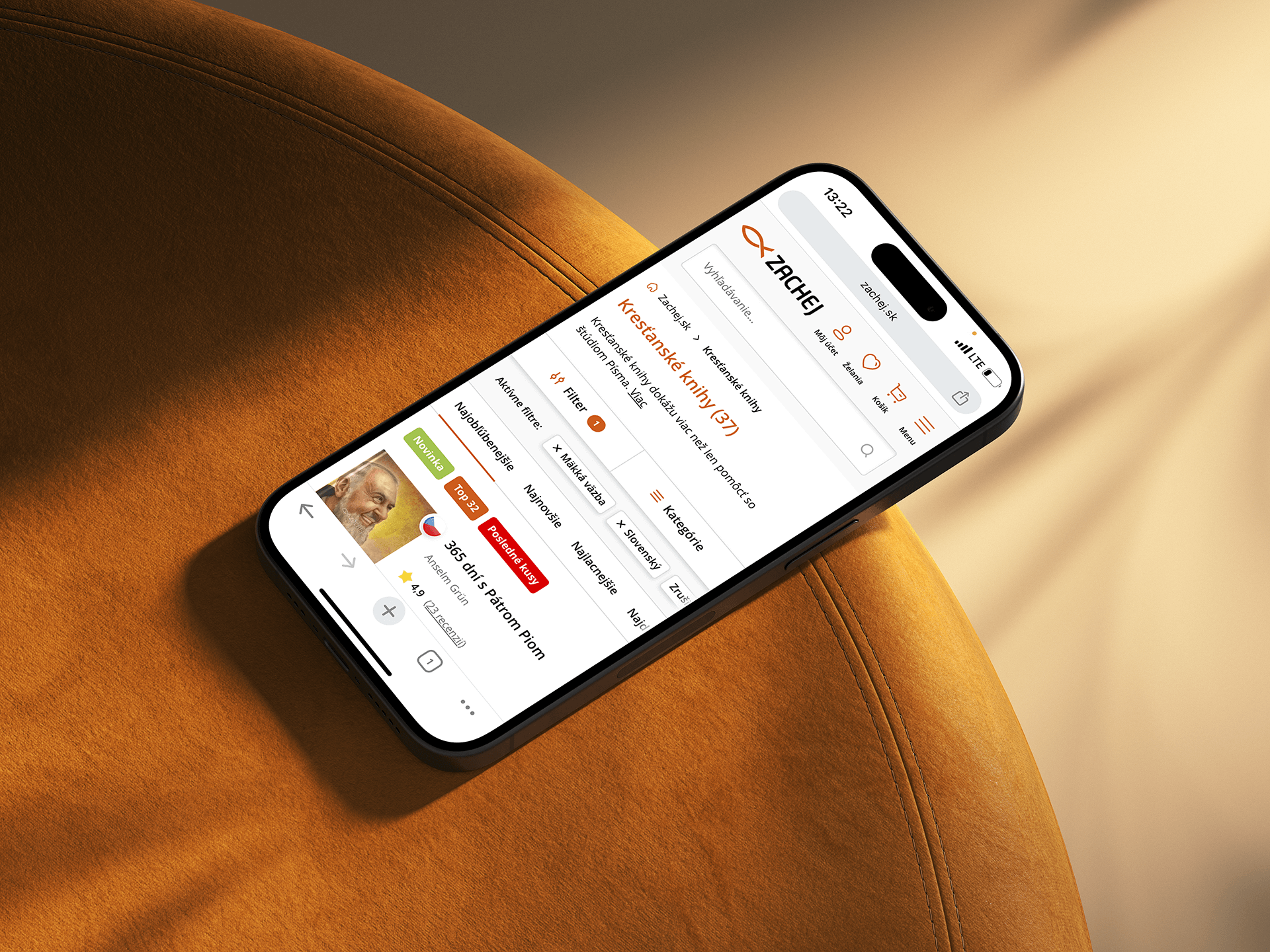
Your brand, your way. Our tailored eCommerce development caters to your specific requirements
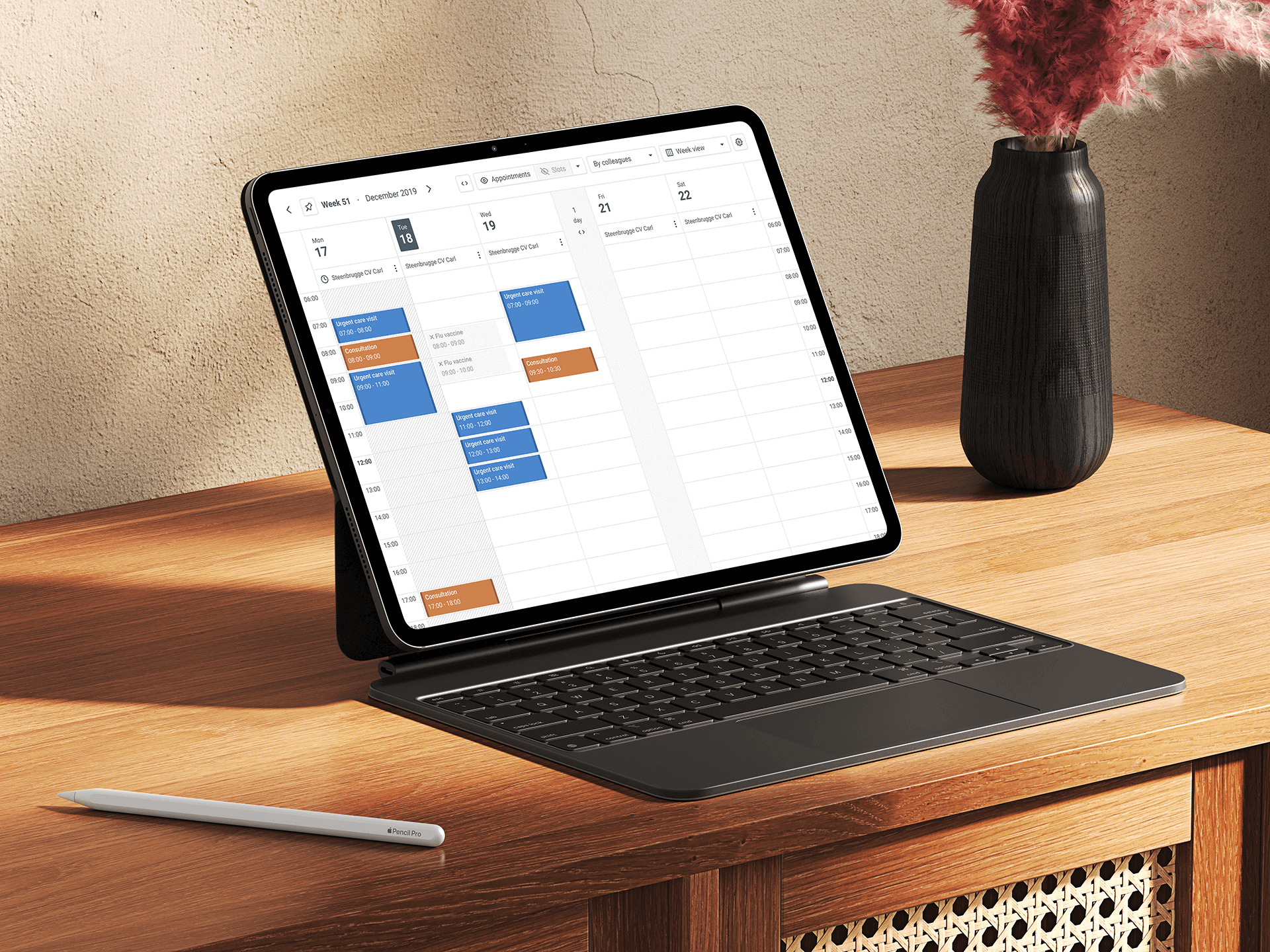
Whether you're envisioning a digital platform or specialized software solution, you can count on us.

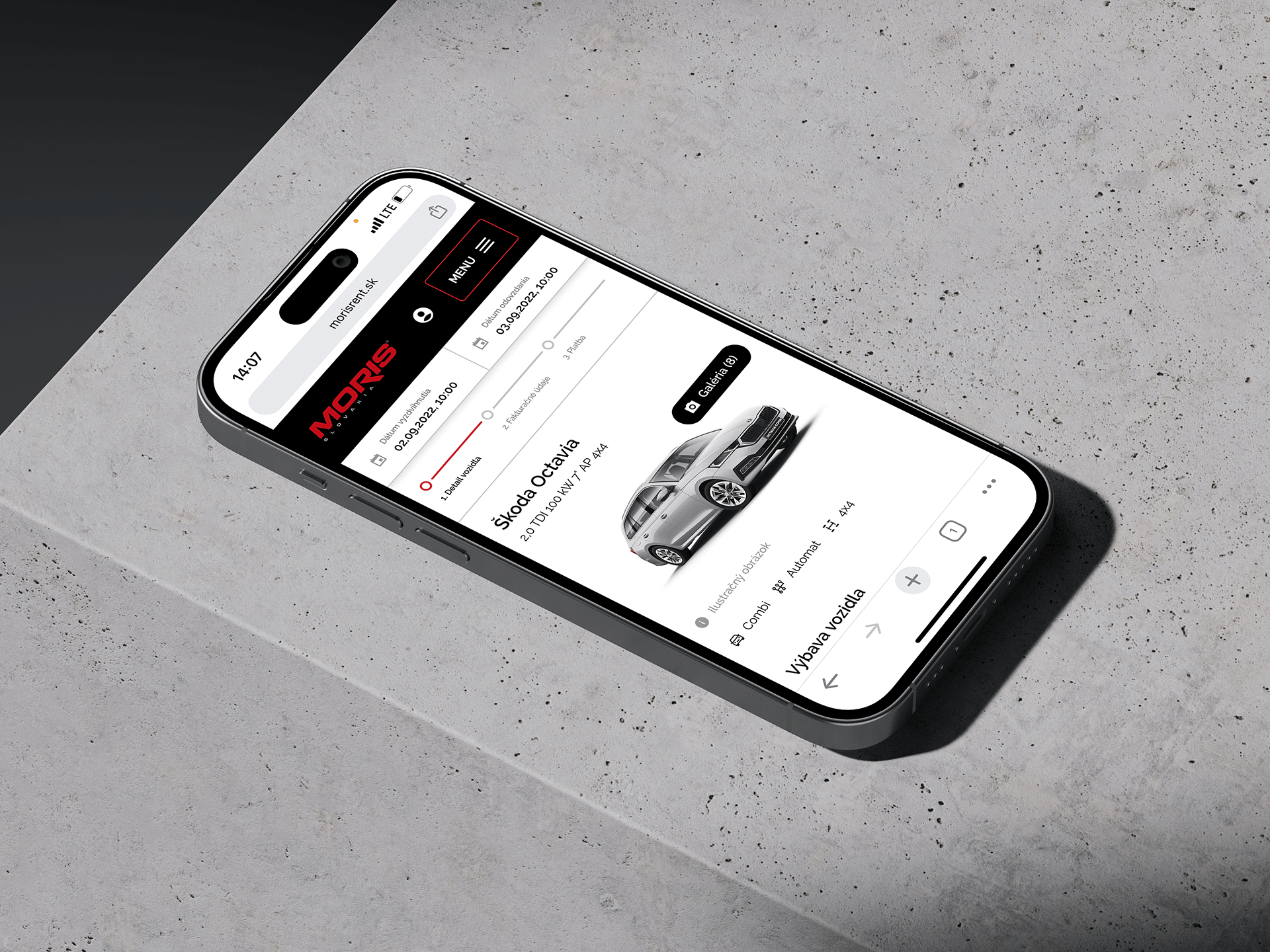
Struggling with the state of your digital product? Let us step in. We are ready to refine, revamp or even start from scratch.




